
You can spend a fortune ensuring that your business is using the best possible solutions available. You can make sure that all your apps and software are regularly updated and upgraded. You can invest in the best anti-virus solutions available. And you could still fall victim to a Zero Day Attack.
What is a Zero Day Attack?
A Zero Day Attack or exploit is one of the most dangerous to businesses. They are cyberattacks that take advantage of a vulnerability – a weakness or flaw in an app or piece of software – before anyone else even realises that it exists. Since even the most expensive anti-virus operates based on available information, a Zero Day attack is often able to fly under the radar, infecting devices and networks without being detected, since it exploits a weakness that only the attackers are aware of. Eventually software creators and app developers will notice the vulnerability and release a patch or update to fix it, but this often occurs after businesses have already fallen victim to attacks.
How Can I Protect My Business From A Zero Day Attack?
It’s because these attacks are so fast-acting that businesses are so vulnerable to them. Even regularly updating your software isn’t enough to keep a Zero Day attack at bay since, by its very nature, a Zero Day exploit occurs before developers even realise that a patch or update is needed. However, while there’s no way to ensure that your company is completely safe from these kinds of attacks, there are Zero Day protection measures that you can take to reduce your business’ risk of falling victim to one.
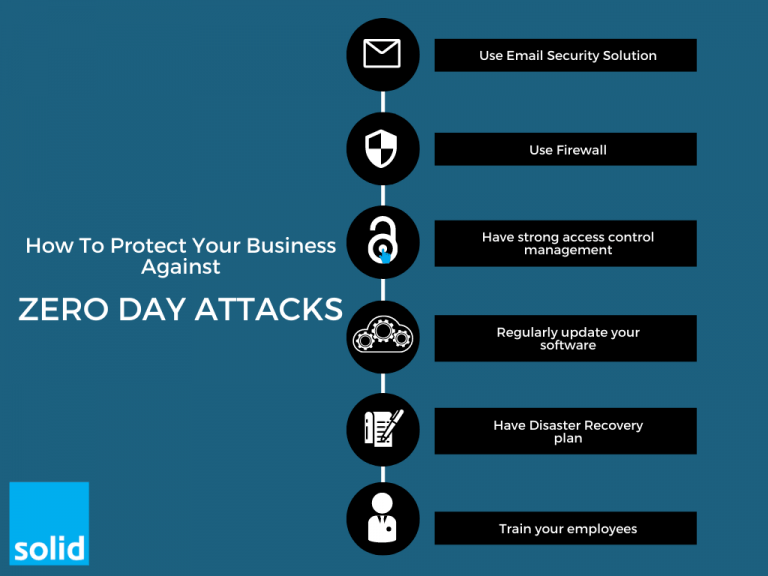
- Make Sure That You’re Using the Right Email Security Solution
One of the most popular ways to infect systems during a Zero Day attack is through malware emails. Having strong email security is essential in combating not just a Zero Day attack, but so many other forms of cybercrime. And when it comes to Zero Day threats, not all email security solutions are equal. You want to make sure that the security system you put in place is able to proactively detect suspicious links and email attachments, even when your traditional anti-virus isn’t aware of any problems. This is where using a email security solution like Microsoft’s Advanced Threat Protection can have a huge impact on keeping your business’ data safe and secure. - Good Training Goes a Long Way
Your teams are your first defence against a Zero Day attack, and making sure that they know how to recognise suspicious links and activity, even when your security systems don’t, could be the difference between a close call and a cry of frustration. Tools like Microsoft Defender for Office 365 can help you train your employees by letting you send out fake phishing emails, and seeing how they respond. This will see you pinpoint areas where further training is needed, and ensure that when it comes to the real thing, your teams are prepared. - Put Up a Firewall
Having firewall security measures in place will help you to restrict access to your network in real-time and prevent a Zero Day attack from infiltrating your systems. Your firewall controls which devices are able to access your servers, and manage the traffic that comes through your network. This means that if an unauthorised device tries to access your systems during a Zero Day attack, they’ll be blocked immediately. Even if an attacker somehow gains access to an authorised user’s credentials, they’ll be limited by the types of traffic your network can send and receive. - Keep Control Over Who Has Access
There are measures that you can take to prevent an attacker from gaining access to your systems at all. And then there are measures that you can take to limit the impact a Zero Day attack can have when cybercriminals do gain access. Having strong rules for access control and management will ensure that even when an attacker does gain access to your network, there is little that they’ll be able to do to it. You’ll be alerted to any suspicious activity straight away, your critical data will remain untouched, and your business operations will continue uninterrupted. - Make Sure That You’re Managing Your Patches
What makes a Zero Day attack effective is that they take place before developers can even realise that their software contains a vulnerability. This means that keeping your software up to date won’t necessarily stop your business from being attacked. But it can help you to limit the impact that a Zero Day attack can have, and put a stop to their threat as quickly as possible. As soon as a patch for the vulnerability becomes available, you want to ensure that it will be implemented across your systems. Keeping your software regularly updated reduces the risk of your becoming a victim to a Zero Day attack, and limits the timeframe that attackers may have to access or corrupt your data. - Have A Plan In Place
Now that you know what a Zero Day attack is, and how it can impact your business, it’s important that you have an incident response plan in place to prepare for one. While it’s almost impossible to stop a Zero Day attack from occurring, you can ensure that your teams know what to do when one occurs. You can put measures in place to restrict an attacker’s access to your data, and can have steps that your employees can follow to ensure that their devices remain safe and secure, stopping attackers from infiltrating your network through them. It’s also important to have a Disaster Recovery plan in place, to ensure that any data that is affected by a Zero Day attack can quickly and easily be retrieved and recovered, all without impacting your business operations.
Solid Systems is the perfect partner to help you with Zero-Day attack prevention. With over 18 years of experience helping businesses to keep their systems safe, we are perfectly placed to help you plan and implement protective measures. When a Zero Day attack occurs, you want us by your side to curb its impact on your company. Contact us today to find out more about our cybersecurity solutions.

