There is no denying that the digital age has revolutionised not only how we communicate with one another, but also how we share information, data, and other resources. In a post-COVID world, where remote working and online learning are the new norm, computer networking has assumed a great deal of significance.
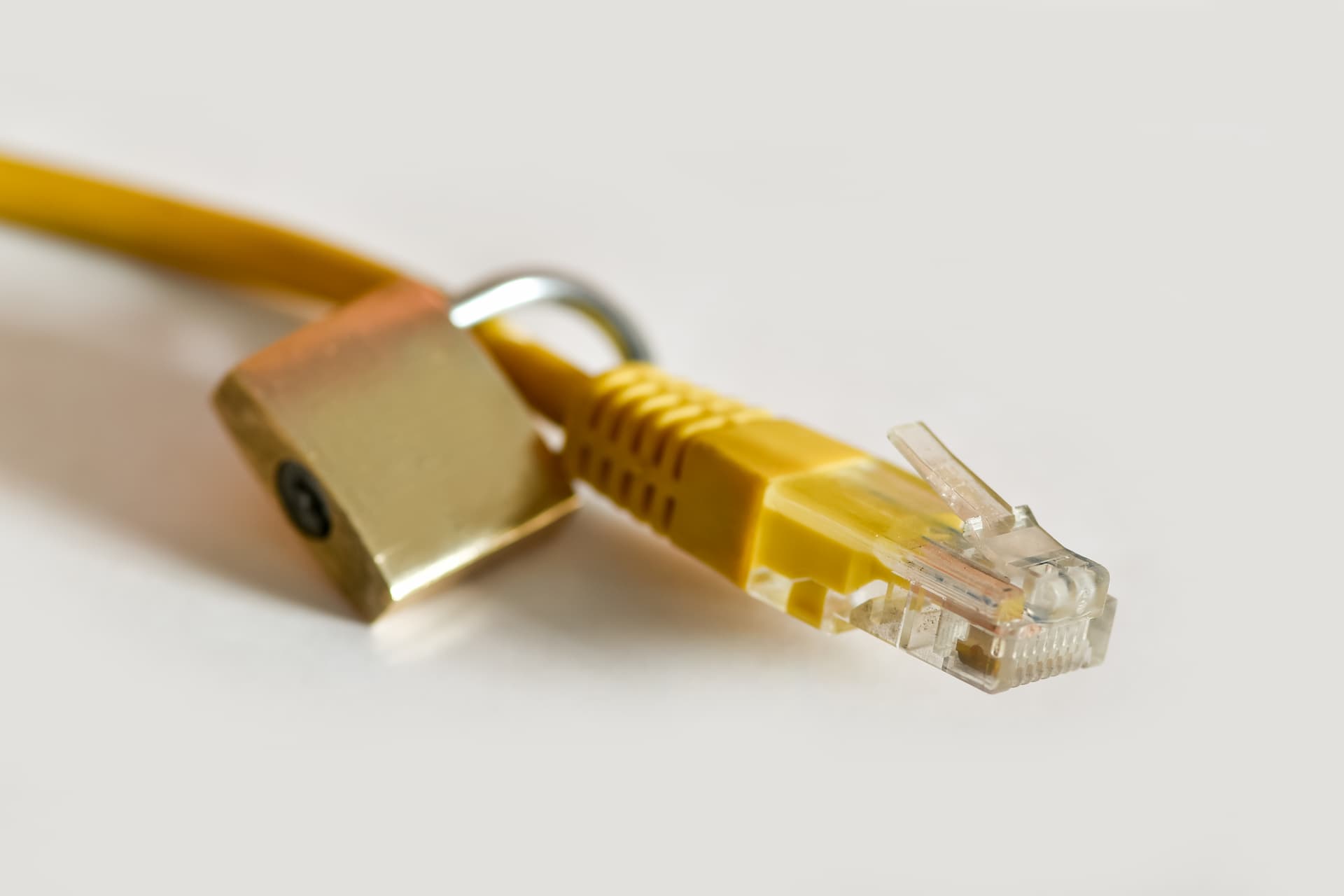
But our shift to this virtual lifestyle has also made us susceptible to cybercrimes. It is estimated that these attacks now cost the world economy more than $1 trillion, showing an increase of over 50% since a 2018 report. The statistics are alarming, and this makes it imperative for businesses to put network security solutions in place.
To put it simply, network security prevents unauthorised access and theft of sensitive data. Its a system of rules and policies that ensure the confidentiality of computer networks, the security of company assets, and the protection of data from various breaches and threats. Network security systems work by authenticating users and permitting only authorised access to network data and resources, preventing intruders from taking advantage of your network.
There are several network security management tools, including technologies, hardware devices, and software applications. Every business, irrespective of size or scale, needs these tools to combat security threats and protect valuable information from cyber criminals. Let’s examine the different types of network security solutions that you can include in your security plan to protect your network.
Principles of Network Security
Before we dive into the types of network security, let’s understand the principles on which these tools function. There are primarily three principles of network security, which are:
- Confidentiality
Sensitive data and vulnerable resources are protected from unauthorised access and misuse. - Integrity
Information is protected from intentional and accidental alterations. This ensures reliability, accuracy, and legitimacy of your data. - Availability
Your data is made available to the people who need to access it, no matter which device they may be using.
Types of Network Security
- Email Security
Emails are one of the biggest concerns when it comes to security breaches. Viruses and malware can easily be introduced into a network through them. These attacks come in a variety of forms, from scams and SPAM, to phishing. That’s why it’s so important to have email security software scan all incoming emails for threats and prevent outgoing emails from sharing sensitive information. - Network Access Control
It is important that only the right people have access to your network and its resources. Network Access Control (NAC) is a set of comprehensive control policies that help you give access to the users who need it, without compromising your data security. It also lets you identify and block devices that are potential threats. Through these security policies, you can monitor your network closely, and manage it more efficiently by even setting limits on the amount of data that each device can access. - Intrusion Prevention Systems
An Intrusion Prevention System (IPS) blocks and reports malicious activity on a network. It also keeps track of malware and prevents outbreaks and reinfections. Having an IPS is particularly useful since it can send alarms when harmful activity is detected, stop malicious data from affecting your network, reset your connection and block traffic from suspicious IP addresses. - Wireless Security
Because wireless networks can be accessed by so many devices, they are immediately more vulnerable to security breaches than wired ones, and need extra attention and protection. Using wireless security protects your networks from malicious attacks and unauthorised access, encrypting and securing all wireless communication by default. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). - Data Loss Prevention
Data Loss Prevention (DLP) technologies keep your resources confidential. They control how much data your users can transfer, stopping valuable information from unintentionally leaving of your network. Your network administrator can limit access to your information and prevent it from being shared with the outside world. This is how DLP technology prevents employees from uploading, forwarding, sharing, or printing valuable information that can put the company at risk. - Virtual Private Network
A Virtual Private Network (VPN) provides online privacy and anonymity by having users connect to your network from wherever they are in the world. Any information downloaded or uploaded between the two points is encrypted, adding a further level of security, and users have to authenticate communication between the device and the network. The encryption not only provides greater security but also hides your Internet Protocol (IP) address, preventing your online activities from being detected. - Behavioural Analytics
Security support personnel spend a good deal of time analysing and defining what normal behaviour for users, apps, and networks looks like. By studying what the norm is, it becomes easier to detect unusual network behaviour. Based on these norms, behavioural analytics tools can quickly identify signs of security breaches, spotting potential problems, immediately isolating threats, and promptly repairing them. - Application Security
Every device and software app that we use in a network is a possible gateway for hackers. This makes it essential to have a network security system that protects every app you use. This is where application security comes in, protecting your hardware and software, and advising on best practices that can maximise your network security.
Ensure the Safety of Your Resources
Its tough to recover from security breaches that compromise your data and sensitive information. To make our virtual lives safer, we should be wary of our actions online and be careful about how we interact on networking platforms. But prevention is always better than cure, and network security measures are essential prevention in this day and age.

