
As technology continues to evolve and businesses rely more on digital systems, the risk of cyberattacks has become a major concern. In fact, according to a recent report by IBM Security, the average cost of a data breach is now $3.86 million USD, or over R72 million.
To prevent disruptions to your business operations and safeguard both sensitive data and your reputation, it’s become necessary for companies to conduct regular cybersecurity audits, which not only identify potential vulnerabilities and risks but also ensure compliance with regulations like South Africa’s POPI Act and the EU’s GDPR, as well as industry best practices.
But what exactly is a cybersecurity audit and how can you conduct one effectively? In this article, we’ll explore the key components of a comprehensive cybersecurity audit checklist and why you need one for your business.
Why Do You Need A Cybersecurity Audit Checklist?
Let’s start off with the very basics – you get that you need to conduct cybersecurity audits on your systems and processes, but why is it that you need a checklist to get it done?
IT audits and IT security audits are detailed and complicated processes. By having a cybersecurity audit checklist, you can make sure that you are taking a thorough look at your systems, your IT infrastructure, your employee training and more, and that you’re addressing any risks and vulnerabilities that your business faces.
This can, of course, be done without a checklist at hand, but having a breakdown of each area that you need to review and address will make the process simpler and more structured, ensuring that no aspect of your cybersecurity goes unchecked.
The Broad Categories In A Cybersecurity Audit Checklist
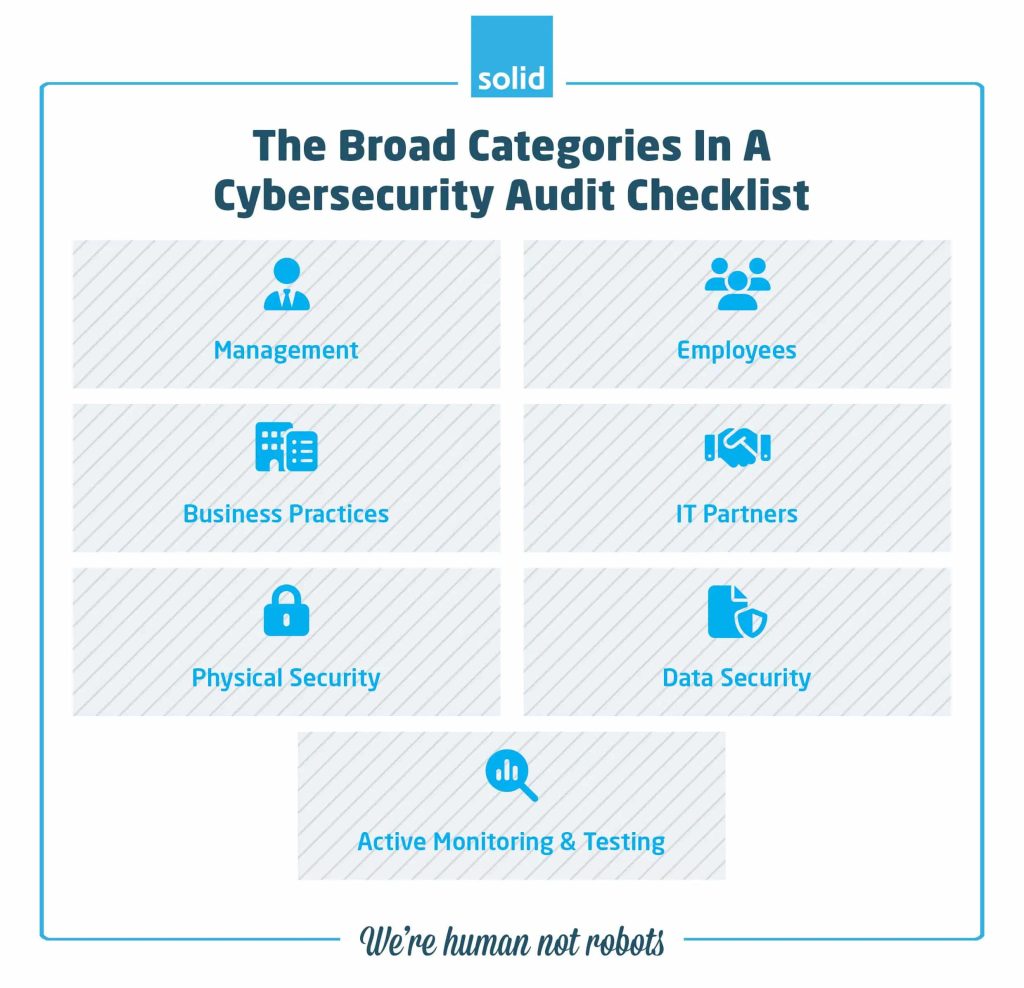
When conducting a cybersecurity audit, it’s essential to cover all aspects of your business that relate to security. These could include:
• Management
Take the time to focus on the role your company’s management plays in ensuring proper cybersecurity measures are in place. This includes evaluating your existing policies and procedures, defining new procedures that will keep your systems, data and humans safe, as well as identifying any gaps or weaknesses that need to be addressed. Items for your checklist could include:
- Have you reviewed your existing cybersecurity policies and aligned them with industry standards?
- Have you detailed the roles and responsibilities in your business when it comes to reporting on and ensuring cybersecurity?
- Do you have a documented incident response or disaster recovery plan in place?
- Have you checked your compliance with relevant regulations like the POPI Act and GDPR?
- Have you allocated a budget for cybersecurity measures and resources?
• Employees
Your humans are the weakest link in your business’ cybersecurity. This may sound harsh, but it’s true. They are your first defence against attack, and you need to make sure that they are thoroughly trained on how to recognise potential attacks, what they should do if one occurs, the latest cybersecurity best practices, and that they understand their role in protecting your business data. Examples of items that should be included in your cybersecurity audit checklist are:
- Do you have ongoing cybersecurity training initiatives in place?
- Do you have protocols in place for reporting security incidents?
- Do your teams have a thorough understanding of threats like phishing and social engineering?
- Do you have a security-conscious culture within your business?
- Do you have onboarding and offboarding procedures in place for managing your employees’ access to company data?
• Business Practices
It’s important to review your business processes to identify any potential risks or vulnerabilities. This may involve identifying areas where data is being collected, stored, processed, or transmitted and ensuring that there are adequate security measures in place at each stage of the process. And for businesses who are embracing remote or hybrid work environments, this may also be a good time to look over your Bring Your Own Device (BYOD) policy to ensure that any devices connecting to your network or accessing sensitive data are effectively secured. It’s also a great opportunity to review your strategy for dealing with Shadow IT – the practice of your humans using apps and services that help them to work more effectively, without your IT team knowing about them or ensuring their protection. Actions that you could check off include:
- Have you reviewed all contracts and agreements with any third-party vendors to ensure that they include relevant security clauses?
- Have you reviewed your policies for employees using their own devices and apps?
- Do you have data classification policies in place, and are they being adhered to?
• IT Partners
If you’re dealing with technology partners, managed IT service providers, cloud providers or any other external IT company to help you manage your technologies, it’s crucial to include them in your cybersecurity audit as well. You’ll want to make sure that you’re not only documenting the different providers that you use and ensuring that your humans understand who to call when IT issues crop up, but that your security policies and procedures are aligned with theirs, ensuring maximum protection across your business and your outsourced IT services. Items for your cybersecurity audit checklist could include:
- Do you have a consolidated list of all of your IT providers?
- Do you regularly evaluate the security posture of existing and potential technology partners to ensure alignment?
- Do you regularly review the data and systems that your IT partners have access to?
- Do you have a procedure in place for offboarding partners and revoking access to data and assets?
• Physical Security
While we often focus on digital threats, physical security is just as important when it comes to protecting your business data. Your cybersecurity audit should include a review of both your physical premises as well as your cloud services, and any access controls that are in place, to ensure that only authorised individuals have access to restricted areas or sensitive information. This may involve reviewing security cameras, keycard systems, and implementing biometric or Multi-Factor Authentication (MFA). It’s also essential to have proper procedures in place for data destruction and disposal, both onsite and within your cloud platforms to prevent any sensitive information from falling into the wrong hands. Examples of items that should be included in your checklist are:
- Do you have an up-to-date inventory of all your physical IT assets?
- Do you have procedures in place for tracking and disposing of physical IT assets?
- Do you have controls in place for managing access to on-premises IT infrastructure and data?
- Are your on-premises or physical assets protected against environmental risks including temperature, humidity, power surges and fire?
- Do you have backups in place to ensure business continuity even in the case of potential failures?
• Data Security
The security of your company’s data is a top priority, and your cybersecurity audit should include a thorough review of all measures in place to protect it. This may include encryption, firewalls, antivirus software, the use of tools like Endpoint for Microsoft 365 and Microsoft Intune, Identity and Access Management (IAM), and cloud backup procedures. It’s also essential to have a Disaster Recovery Plan in place to deal with potential data breaches or even natural disasters, as well as regular backups and testing to ensure the integrity and availability of critical information. Your cybersecurity audit checklist could include items like:
- Do you have encryption protocols in place for protecting critical information both in transit and while it’s stored on your servers?
- Do you have an Identity and Access Management tool in place to help you control permissions for employees throughout your business?
- Do you have tools in place that can alert you to unauthorised access attempts?
- Is your data being gathered, stored and processed in compliance with relevant regulations?
- Do you have endpoint protection in place to ensure that any devices accessing sensitive information are able to be wiped remotely if an employee leaves your company?
• Active Monitoring And Testing
One of the most critical aspects of cybersecurity is continuous monitoring and testing. Your audit should include an evaluation of your current monitoring processes and procedures, as well as any tools and technologies in use. This may involve conducting penetration testing to identify vulnerabilities, implementing intrusion detection systems, and using security information and event management tools to monitor for potential threats. Examples that you could incorporate into your checklist include:
- Do you have a policy in place for regularly reviewing potential vulnerabilities to your systems?
- Do you have tools in place for patch and update management on in-office as well as remote devices?
- Do you run regular simulations of real-world attacks to gauge your employees’ responsiveness and readiness?
- Do you have a system in place for reporting potential security incidents?
How Can You Conduct A Cybersecurity Audit?
Now that we’ve covered the broad categories of a cybersecurity audit checklist, let’s take a closer look at how you can conduct one for your business. These steps will help ensure that your audit is thorough, comprehensive, and effective in identifying potential cybersecurity risks and vulnerabilities.
• Define The Scope Of Your Audit
The first step to conducting a cybersecurity audit involves determining which assets, systems, and processes are within the scope of the audit and which are not. This will help you focus your efforts and resources on the areas that need the most attention.
Why not include everything within your cybersecurity audit checklist? Well, not all systems are equal. Processes and policies that are used and referred to on a daily basis are going to be more critical to your cybersecurity than those that come up once or twice a year, for example. Or if your company recently undergone a cloud migration, you may still have older on-premises backups which are going to become defunct in the near future, where protecting your cloud environment will take a higher priority. That’s not to say that you’ll want to ignore those on-premises backups entirely, but you may want to spend less time on them if you are going to be deleting them altogether in the coming months.
• Decide On The Framework That You Want To Use
There are a number of different approaches that you may want to take when it comes to your cybersecurity audit. One of the most popular methods is the Confidentiality, Integrity, and Availability (CIA) model, which focuses on effectively managing access to your systems, ensuring that your data is protected from both internal and external threats, and optimising your business continuity.
But while the CIA model may be the most popular, that doesn’t necessarily mean that it’s going to be the right approach for your business to take. This is why many companies choose to consult with IT experts before undergoing a cybersecurity audit, or to have a managed IT service provider conduct the audit on their behalf, ensuring that the process is done in a way that will both keep them protected and most closely align with their needs and goals.
• Ensure Cross-Departmental Communication
Cybersecurity is a company-wide responsibility, and it’s crucial to involve all relevant departments in the audit process. This includes IT, finance, legal, human resources, and any other department that has access to sensitive data or plays a role in maintaining the security of your systems. By involving all departments, you can gain a holistic view of potential risks and vulnerabilities within your business.
• Know Your Compliance Standards And Regulatory Requirements
Compliance standards and regulatory requirements may vary depending on your industry, location, and specific business operations. It’s essential to have a clear understanding of these standards and requirements before conducting a cybersecurity audit. This will help you identify any gaps in your current security measures and ensure that you are meeting all necessary regulations.
• Map Your IT Infrastructure
To conduct an effective audit, you need to have a clear understanding of your company’s IT infrastructure. Map out all hardware, software, networks, and data storage systems that your business uses, allowing you to identify potential entry points for cyberattacks. This is, once again, where Shadow IT is going to also play a role, since you’ll want to make sure that you have as thorough an understanding as possible of the apps and software that your humans are using, what data those apps need access to, and how they can be protected.
• Identify And Address Vulnerabilities And Risks
During the audit, it’s crucial to identify any vulnerabilities and risks within your systems. This could include outdated software, weak passwords, lack of data encryption, or inadequate security protocols. Once these are identified, take immediate action to address them and strengthen your overall security posture.
A cybersecurity audit is also an opportunity to evaluate the processes that you’ve put in place for dealing with or mitigating risk to your business. You’ll want to assess the effectiveness of existing policies, procedures, and controls, and make necessary adjustments and updates to improve your risk management strategy.
• Set Priorities For Your Cybersecurity
Once you’ve conducted your audit (with or without the help of a cybersecurity audit checklist), you’ll have a better understanding of your cybersecurity standing, and will be able to prioritise areas that require immediate attention. This could include implementing new security measures, updating existing ones, and training employees on best practices for cybersecurity. By setting priorities, you can allocate resources effectively and ensure that the most critical areas are addressed first.
• Perform Regular Audits
Cybersecurity is a constantly evolving field, with new threats emerging all the time. It’s essential to conduct audits at least once a year, to stay on top of potential vulnerabilities and risks. This will help you identify any new areas that need attention and ensure your security measures are up to date.
How Long Does A Cybersecurity Audit Take?
Because no two businesses are the same, it’s impossible to predict how long a cybersecurity audit will take to complete. It can be anywhere from a few weeks to several months, and the timespan will also depend on whether you’re taking on the challenge on your own, or have a technology partner by your side leading you through the process.
When you work with cybersecurity experts, they will have a better understanding of the scope of your cybersecurity audit, and will have procedures of their own in place for conducting one as efficiently and effectively as possible. Whereas when you take an audit on internally, the process is likely to take longer as you try to gain a detailed understanding of each aspect of your IT. Conducting your own audit without help from professionals will also often see your humans being taken away from their day-to-day activities as they focus entirely on auditing your systems and processes.
And all of this is not taking into account the time that would need to be spent implementing any recommendations that arise as a result of the cybersecurity audit, which in themselves can take weeks or months to put in place.
How Can Solid Systems Help?
As a technology partner with a focus on cybersecurity, Solid Systems is perfectly placed to assess your company’s cybersecurity needs. Our Solid Systems Review is specifically designed to review your IT infrastructure, your systems and your policies and ensure that they not only meet our certified standards, but are in line with cybersecurity best practices. But our reviews also go beyond just a simple cybersecurity audit, encompassing strategic technology roadmapping, detailed documentation, training, and so much more. We want to make sure that you are not only implementing the right solutions for your unique business needs, but are boosting their adoption throughout your company, have them configured in the right way to maximise your protection, and have are addressing any risks and vulnerabilities as quickly and effectively as possible.
Want to find out more about our Solid Systems Review and what it entails? Book a Systems Review Discovery with our Sales team and start working with a strategic technology partner who will ensure that your IT is adding maximum value and protection to your business.
Frequently Asked Questions
Popular Searches
- Preventing Cyber Attacks
- IT Company in Cape Town
- Data Security & Integrity
- Cybersecurity Tips For Employees
- IT Company in Sandton
- Cloud Security Best Practices
- IT Company in Polokwane
- IT Company in Midrand
- What is Data Breach
- IT Company in Durban
- IT Company in Pretoria
- What Is Cyber Espionage
- Audit and Compliance
- IT Company in Gauteng
- Business Cyber Hygiene Checklist
- IT Company in Centurion
- IT Company in Johannesburg

